Table of Contents
Introduction
In today’s technology-filled world, everyone has become dependent on the network. From online shopping to online business, whether it’s using the internet for personal use or online work (like freelancing), everything depends on the network. Now, if hackers hack the network, there are very high chances that all your data, personal files and photos, personal information will be stolen.
Therefore, understanding networks is crucial when learning ethical hacking and cybersecurity. This will help us understand what networks and network security are, how many and what are their components, what are common attacks, and what tools and techniques are used.
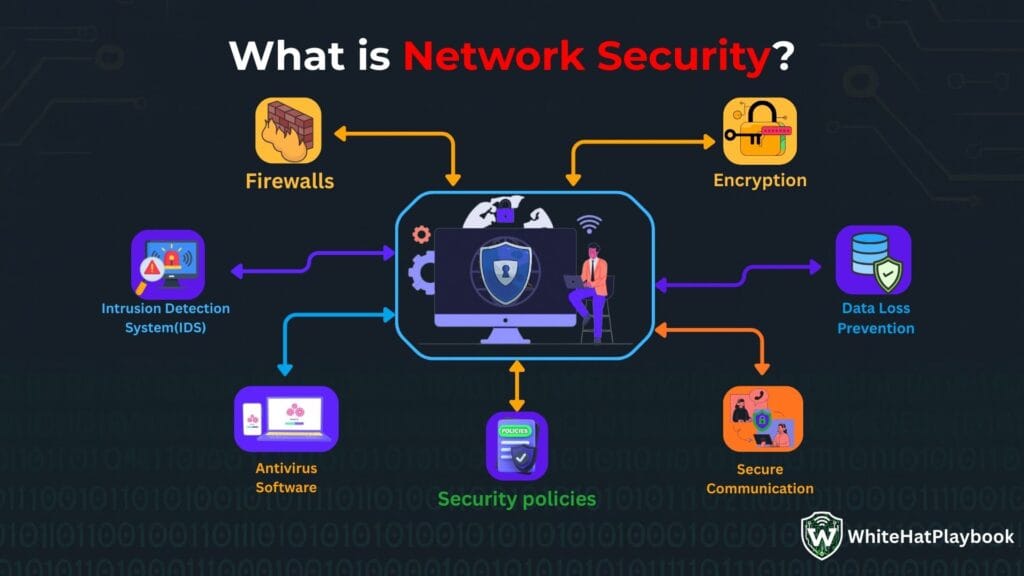
What is Network Security?
Network security simply means that we have to secure our computer network from malicious attackers or black hat hackers. So that no malicious hacker can gain unauthorized access to our network and steal and misuse our system data and perform any attack on our system.
Why Network Security is Very Important?
Network security is crucial today to protect our data and systems. Because:
Visit For More About Why Network Security Is very Important: Top 10 Free and best Penetration Testing Tools (2025) | Full Guide
- Sensitive Data Protection: Companies or organizations have a lot of individually sensitive data (such as passwords, personal files, financial records, and many business secrets). Network security is crucial to protect it from malicious hackers.
- Protection against unauthorized access: The job of network security is to make sure that no one can get unauthorized access to our systems and network, and only authorized users can access the network and computer systems.
- Protection Against Cyber Attacks: Network security is very important to keep the networks of companies or organizations safe from cyber-attacks (like malicious hacking, DoS/DDoS attacks, malware or ransomware, phishing, and many more).
- Business Continuity: Network security ensures that companies can access all services without interruption, as network attacks such as malware, DDoS, or network breaches can disrupt business operations, slowing or halting personal communications and business operations.
- Legal & Compliance Reasons: Network security is very important for the security compliance of companies, so that the data of the companies is not leaked and no legal action or heavy fines are imposed on them.
- Protection from financial loss: Network security protects companies and organizations from financial and reputational losses caused by cyber-attacks.
- Build Trust: If the network is secure, then customers/clients and users develop trust in the companies, which is very important for companies and small and new startups in today’s digital era.
Network Security layers/Components
Generally, there are 7 main layers of network security. Network security layers are divided into two models called OSI model and Defense-in-depth. OSI model arranges network functions into 7 layers (Physical, Data Link, Network, Transport, Session, Presentation, Application) for technical understanding. Whereas defence-in-depth model is used for multiple measures (like physical security, network security, endpoint security and application security) to protect against threats.
OSI Model:
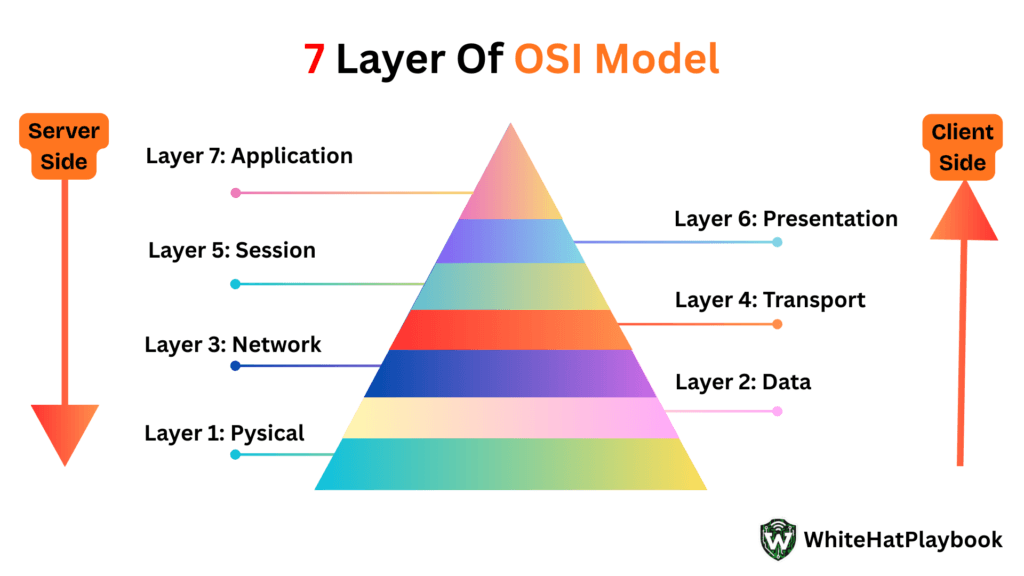
- Physical layer: The physical layer is the last layer. Its main function is to transfer bits (0 and 1) through hardware (such as wires, cables, and connectors). If the physical layer fails, no communication is possible.
- Data Link layer: The data link layer establishes and terminates communication between two directly connected devices (such as Ethernet, ARP, Switches). Its main function is to transmit packets from source to destination by dividing them into frames. The data link layer has two sub-layers called LLAC (Logical Link Control) and MAC (Media Access Control).
- Network layer: The main function of the network layer is to secure the data and find the best route for the data packets to reach from the source to the destination.
- Transport layer: The transport layer manages the data flow and ensures that data reaches the receiving device safely. The transport layer can also handle errors if they occur.
- Session layer: The main function of the session layer is to establish communication between two devices (sender and receiver), called a session. It also authenticates, synchronizes, and terminates the session.
- Presentation layer: The presentation layer converts the data into an understandable format so that the sender and receiver can understand the data.
- Application layer: The application is the first and closest layer to the user, as it is the layer through which the user can access all the services of the network. Its functions include file transfer, email services, web browsing, and network service requests.
Défense-in-depth:
- Physical security layer: The physical security layer controls access to the physical infrastructure where networks and systems are installed.
- Network Security Layer: This layer monitors network traffic, protects it, and controls access to it.
- Endpoint / Host Security Layer: This layer works to secure all our individual devices (like computers, smartphones, laptops, servers) connected to the network.
- Application Security Layer: Applications focus primarily on software and applications. It works to protect them from attacks.
- Data Security Layer: The primary target of hackers is data theft, so this layer is considered extremely critical. Its primary focus is on protecting data through encryption, backups, and data loss prevention measures.
- Identity & Access Management (IAM) Layer: The main function of this layer is to ensure that only authorized users and devices have proper access to the network.
- Policies, Procedures & Awareness Layer (Human Layer): The human factor is considered the weakest link, so this layer serves users and employees. Users and employees are informed about security policies, trained, and informed about incident response plans.
Common Threats & Network Attacks
Network security is increasingly important today due to threats and network attacks. Some common threats include:
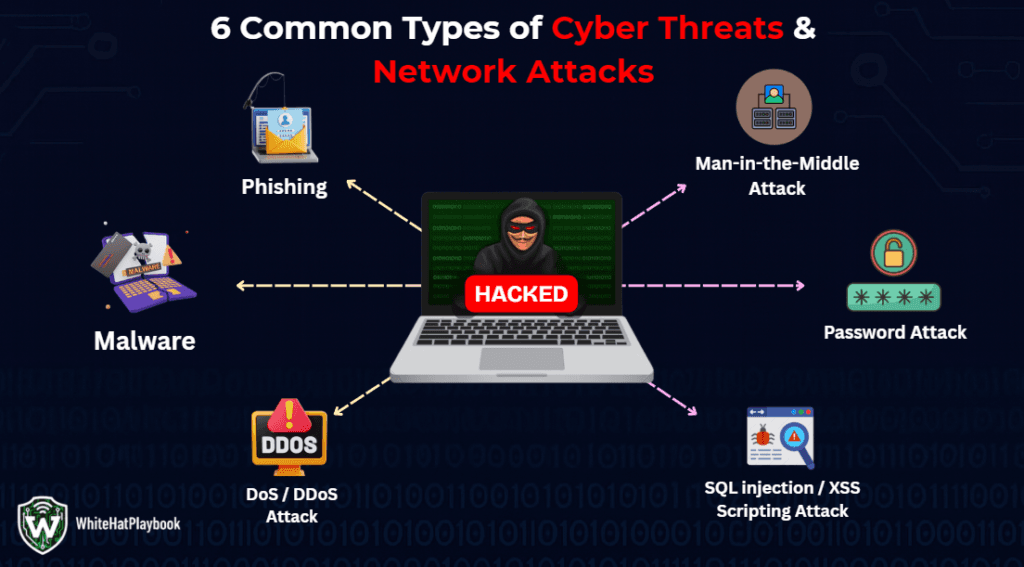
- Malware / ransomware: Hackers can perform this attack to steal and corrupt entire systems. Hackers can also sometimes lock our systems using this attack.
- Phishing: Phishing is a part of social engineering attack, in which the attacker tries to steal sensitive information of the user by creating fake emails, messages or websites on the target device.
- Man-in-the-Middle (MitM): In a Man-in-the-Middle attack, the attacker can secretly stay between the client and the server, listen to all the communications between them, steal all their data and even modify them.
- Denial-of-Service (DoS) / Distributed DoS (DDoS) Attacks: In this attack, the attacker overloads the network and services of the targeted device, making all the services of the system and network unavailable.
- Password Attacks: The attacker attempts to crack the system’s password by using multiple password attacks (e.g., brute-force, dictionary) to gain access to the target system and steal the system’s credential information.
- SQL Injection: In SQL injection attack, the attacker can inject malicious SQL code into the input fields (like login form, search box, URL parameters) of the web application to read, modify and even delete the user’s database.
- Cross-Site Scripting (XSS): This is a web security vulnerability attack in which the attacker injects malicious JavaScript code into a website, and if the user opens the website on their device, the script is executed in the user’s browser.
Conclusion
Network security is not a static field today, as networks are becoming increasingly complex with advancing technology. This can lead to new threats. For beginners, adopting layered security, best practices, and continuous vigilance may be the best option. These options can keep networks and data extremely safe.
For further and deeper knowledge and learning, visit our website Whitehatplaybook.com. We will take full care to make our website the best learning platform for both beginners and professionals.
FAQs
- Firewall Security
- Intrusion Detection & Prevention (IDS/IPS)
- VPN & Encryption
- Access Control & Authentication
- Endpoint Security
- Malware & Ransomware: It steals the data of our system, can corrupt them and can also lock our system.
- Phishing attacks: This is a part of social engineering, which tries to extract sensitive information from the user by creating fake emails and messages and sending them to the user's system.
- DDoS attacks: It overloads the network of the targeted system and device and disrupts all network services.
- Man-in-the-Middle (MitM) attack: In which the attacker remains hidden between the server and the client and can listen to the communication taking place between them, can steal the data and can also modify it.
- SQL Injection & XSS: It injects malicious code into the input field of the web application, which when the user runs in his browser, the code gets executed in his browser.