Table of Contents
Introduction
In today’s digital world, as technology advances, so too do threats like cybersecurity attacks and cybercrime. If a company’s network or system is too weak, it can be hacked or exploited at any time, leading to leakage and theft of all the company’s data. Consequently, cybersecurity has become a necessity for everyone from small startups to large organizations and companies.
In today’s article, we will learn about the top penetration testing tools that we can use to test systems. Using this, an ethical hacker tests the system, finds vulnerabilities in them, exploits them and prepares a report and gives it to the company, so that the company can fix those vulnerabilities.
What is Penetration Testing?
Penetration Testing is a simulated cyber-attack that is only conducted with the legal authorization of the company. In Penetration Testing, companies or organizations use ethical hackers (whose main job is to secure the system) to attack and test their systems. This allows the company to identify vulnerabilities within their systems and networks so that they can fix them.
How many Phases in Penetration Testing?
Penetration testing basically takes place in five phases. In these phases, ethical hackers use certain tools to hack the systems for testing and then prepare a report and submit it to the company.
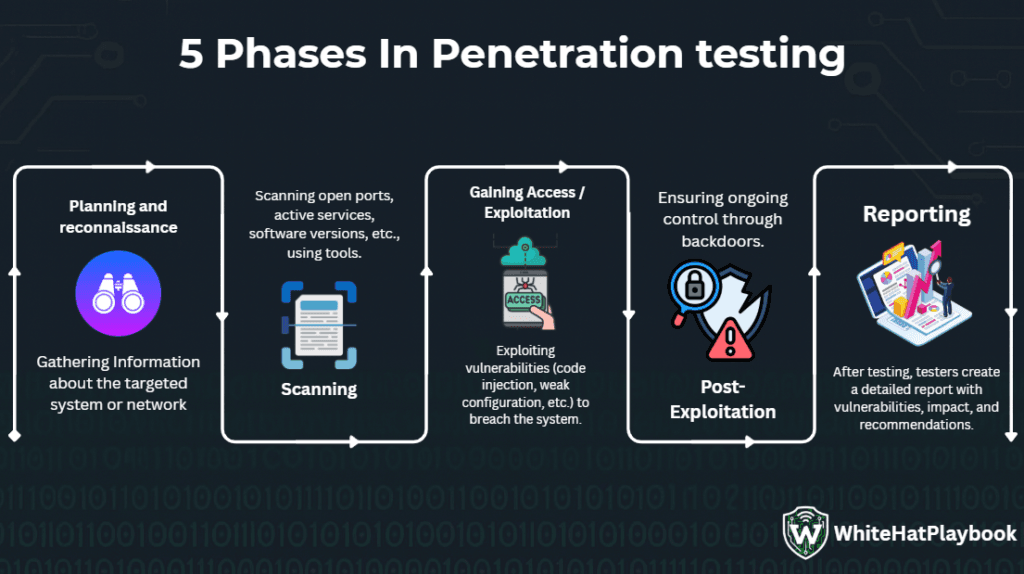
- Planning and reconnaissance: In this phase, ethical hackers first determine the goal and scope of the system to be tested. The pen tester gathers information about the target system to identify its vulnerabilities.
- Scanning: Using tools like vulnerability scanners, the Penetester scans the system for open ports, active services, and potential vulnerabilities and identifies them.
- Gaining Access / Exploitation: If the Pene tester finds any vulnerabilities, they can exploit them using multiple pen testing techniques (such as SQL injection, cross-site scripting (XSS)).
- Post-Exploitation: After gaining access to the system, the Pene tester checks whether he can maintain the access so that no attacker can exploit the weakness and hack them.
- Reporting: After doing all the testing of the system, the Pene tester prepares a detailed report of the entire testing. In this, the Pene tester2 tells the company what vulnerabilities there in their system are, what impact they can have on the system and how they can be fixed.
Top 10 Free and Open-Source Penetration Testing Tool
Here are the top 10 best free and open-source penetration testing tools that will be extremely useful for everyone from beginners to expert Pene tester to test systems.
1. Kali Linux
Kali Linux is completely open source and the ultimate toolkit for ethical hackers and Penetesters. It is developed by Offensive Security. Kali Linux is a Debian-based Linux distribution specially designed for penetration testing and digital forensics. Kali Linux comes pre-installed with 600+ security and penetration testing tools, allowing hackers to perform everything from reconnaissance and vulnerability assessment to password cracking.
Kali Linux Tools: – https://www.kali.org/tools/
| PROS | CONS |
|---|---|
| 600+ Pre-installed Tools For security aur pen testing. | Kali Linux can be difficult for beginners. |
| Kali Linux Is Free, Open-source and Ultimate Toolkit for Ethical hackers. | Kali is not safe for general use because it was created especially for OS hacking and security testing. |
| Along with PCs, it also supports cloud, VS, Docker, VSL, and ARM devices like Raspberry Pi. | If testing is done without permission, then it is considered illegal. |
| Live USB booting available. | Setting up persistence can be tricky. |
| You can create an ISO image of Kali Linux as per your requirement. | Some hardware (such as Wi-Fi adapters and graphics cards) may have compatibility issues. |
| It has Encrypted Persistent Storage (LUKS) support, which makes your data secure. | Kali Defaults has root access, which can be a security risk if misconfigured. |
| Multi-language support is available in Kali Linux. | For beginners, documentation can be overwhelming or too technical. |
| Kali Linux’s own patched kernel, optimized for pen testing. | Despite regular system updates, bugs and compatibility issues can sometimes occur. |
| Kali Linux regularly updates its system and tools. | Tools like Metasploit, Wireshark use a lot of CPU and RAM, which can make them run very slow on low-spec machines. |
Kali Linux: – https://www.kali.org/
2. Nmap
Nmap whose full form is Network Mapper. Nmap is a free and open-source tool that comes pre-installed in Kali Linux. Nmap is currently available on its own website nmap.org. Nmap is used to send IP packets so that hackers can locate hosts and services.
Nmap is one of the first tools used by ethical hackers and Pene testers because Nmap understands the network and sends raw IP packets to it, which helps hackers to identify open ports and services. This helps hackers to find entry points to enter the system and network.
| PROS | CONS |
|---|---|
| Nmap is a completely free and open-source tool, also available on Nmap.org. | It is a bit difficult for beginners to understand and master the Nmap. |
| Scanning becomes very easy with the help of Nmap. | There is a risk of detection in IDS, IPS and firewall. |
| Vulnerability detection can also be automated using the Nmap Scripting Engine (NSE). | Sometimes, some scan results may be incorrect due to firewalls. |
| Nmap can quickly scan even large networks. | Some unwanted network scans can also cause system crashes. |
Nmap: – https://nmap.org/
3. Metasploit
Metasploit is a powerful penetration-testing framework and open-source tool developed by Rapid7. It is a completely free tool and has flexible features, making it very useful for beginners. You can use Metasploit to check whether a system or network is vulnerable or not.
Metasploit has many in-built tools (such as exploit modules, payloads, auxiliary modules, post-exploitation tools). Using this, if the system is vulnerable or outdated, hackers can gain access to the system by exploiting it with Metasploit. By creating custom exploits using scripting (like ruby, python and bash (Shell Scripting)), hackers can also gain remote shell access with advanced post-exploitation tools like Meterpreter.
| PROS | CONS |
|---|---|
| All the tools like exploits, payloads, post-exploit models, auxiliary models, etc. are available on a single platform. | Initially, it may take time for beginners to understand and learn. |
| Metasploit is a completely free and open-source tool. | The paid version of Metasploit is very expensive. |
| Automating scanning/exploitation using built-in models can make the penetration testing process faster. | Complex target systems will require customizations, manual scripting, and deep knowledge from users. |
| Metasploit includes a graphical user interface (GUI), enabling use on Linux, Windows, and macOS. | Ethical hacking is considered illegal if performed on real systems without permission. This poses a significant risk. |
4. Aircrack-ng
Aircrack-ng is a software suite of tools used by hackers to audit the security of Wi-Fi networks or conduct penetration testing. These tools allow testers to verify the security of a network. Aircrack-ng allows testers to capture packets, analyze the network to identify weaknesses, and recover lost Wi-Fi network keys.
| PROS | CONS |
|---|---|
| This tool is free and open source for basic use. | Using this tool with a GUI (Graphical User Interface) can be a bit tricky. |
| Different modules like sniffing, injection, cracking, decryption are available in this tool. | Cracking a strong network like WPA2 is very difficult. |
| It is the best tool for auditing Wi-Fi networks and recovering lost passwords. | Using this tool on a real network without permission is considered illegal. |
| With its help, the tester can also do advanced testing like sniffing or packet injection. | Not all Wi-Fi adapters are compatible with monitor mode, which can cause the hacking to fail. |
| This tool is available for Linux as well as Windows and macOS. |
Aircrack-ng: – https://www.aircrack-ng.org/
5. Wireshark
Wireshark is a popular, free, and open-source packet/network traffic analyzer tool. Using Wireshark, we can analyze captured logs of real-time traffic to learn about protocols, trace their sources, and more. Wireshark can be run on Linux, Windows, and macOS.
| PROS | CONS |
|---|---|
| This tool explains each packet in detail, which is very useful for network troubleshooting and security auditing. | It may take time for beginners to understand these tools because they do not know much about protocols and network structures. |
| It captures packets live and can also load the captured log for offline analysis. | When capturing live data, many packets are received, which can be very difficult to analyze manually. |
| This tool is compatible with Windows, macOS, and Linux. | If there is a weak system and heavy network traffic, then the system may get overloaded while capturing data. |
| It is a very useful tool for multiple purposes like troubleshooting, security audits, educational purposes etc. | This tool doesn’t alert you to ongoing attacks while analyzing traffic. You have to manually look for them. |
| This tool can support TCP, UDP, DHCP, DNS, and many more protocols. | Without the key, encrypted traffic data will not be read. |
Wireshark: – https://www.wireshark.org/
6. OWASP ZAP
ZAP means Zed Attack Proxy – This is an open-source web application security scanner tool developed by OWASP (Open Web Application Security Project). Its special feature is that it is easy to use for both experienced testers and beginners. With the help of this tool, the tester can scan for passive and active vulnerabilities and intercept requests.
7. SQL Map
SQL map is an open-source and powerful penetration testing tool. This tool finds and exploits SQL injection vulnerabilities in a website’s database. Using SQL map, a tester can try different techniques (such as error-based injection, time-based injection, etc.) to find the vulnerability.
If a website or web application has a vulnerability, an attacker can create a database using SQL maps, dump data, or gain access to shell and system files with a weak configuration.
| PROS | CONS |
|---|---|
| Automated SQL injection detection helps in finding vulnerabilities quickly. | The command-line of this tool can be a little difficult to understand in the beginning. |
| SQL Map supports multiple databases – such as MySQL, PostgreSQL, Oracle, SQLite, etc. | Using this tool on websites and applications without permission is considered illegal hacking. |
| With the help of this tool, along with vulnerability detection, extracting data, accessing filesystem and database fingerprinting are also possible. | If the user doesn’t have complete knowledge of the structure and database, then the output obtained may be difficult to understand. |
| SQL map is a flexible and customizable testing tool. | SQL Map’s output may also be inaccurate due to security reasons such as web application firewalls and input filters. |
| Users get regular updates in SQL Map and get support from the community and developers. | If the site’s developer correctly identified the vulnerability as existing, the attack fails. |
8. Hydra
Hydra is a powerful and fast password cracking tool. This tool allows testers to perform brute force and dictionary attacks. This automated tool tries different usernames and passwords at the website’s login prompt to guess their credentials so that the attacker can log in to the website.
Hydra is basically used for ethical hacking. With its help, hackers can easily identify weak password policies and insecure logins by creating custom wordlists and allowing modular extensions. Hydra supports multiple protocols (like FTP, HTTP, TCP/IP, etc.) and services (like DNS and DHCP). It tests whether there is a vulnerability in them or not.
| PROS | CONS |
|---|---|
| Hydra is a scripted tool that uses a wordlist to continuously perform login attempts, which saves time. | Hydra fails if the password is strong and complex. |
| Hydra can support all types of protocols and services including SSH, FTPS and web login. | Hydra can fail repeatedly due to complex passwords and large wordlists, which can also waste tester time. |
| Hydra is a completely free and open-source tool, with no licensing or cost restrictions. | If Hydra repeatedly attempts to attack a strong and monitored system, it is not considered safe. |
9. Nikto
Nikto is an open-source tool as well as a lightweight web server scanner tool. Web applications are at great risk to security as Nikto can scan for 6000+ known issues and misconfigurations. This tool is designed to identify common security issues like misconfigurations, outdated software and dangerous files and scripts against the server.
10. John The Ripper
John the Ripper is famous for fast password cracking because it can make password cracking extremely fast by utilizing multi-core CPUs and GPU acceleration. Both basic and premium versions of this tool are available. This tool is pre-installed in Kali Linux.
The tester uses this tool to automate the guessing process using various techniques (such as brute-force, hybrid, and wordlists). It is primarily used by ethical hackers and penetrators to check password weaknesses.
Conclusion
Ethical hackers use these penetration testing tools to secure the systems of companies and organizations. This makes their systems strong, so that no black hat hacker or attacker can attack them by knowing their weaknesses.
With the help of these top 10 free and open-source penetration testing tools, both beginners and professional hackers can find vulnerabilities, test them by exploiting them and report them to the company.
If you want to gain more knowledge about ethical hacking, then explore our blogs “Blog – Online Programming Course“
FAQs
- Planning and reconnaissance: In this phase, ethical hackers first determine the goal and scope of the system to be tested. The pen tester gathers information about the target system to identify its vulnerabilities.
- Scanning: Using tools like vulnerability scanners, the Pene tester scans the system for open ports, active services, and potential vulnerabilities and identifies them.
- Gaining Access / Exploitation: If the Pene tester finds any vulnerabilities, they can exploit them using multiple pen testing techniques (such as SQL injection, cross-site scripting (XSS)).
- Post-Exploitation: After gaining access to the system, the Pene tester checks whether he can maintain the access so that no attacker can exploit the weakness and hack them.
- Reporting: After doing all the testing of the system, the Pene tester prepares a detailed report of the entire testing. In this, the Pene tester2 tells the company what vulnerabilities there in their system are, what impact they can have on the system and how they can be fixed.
- Port Scanners: This is the first step of penetration testing, also known as reconnaissance and information gathering. This process helps us determine the open ports on the network, including which services are active, the version of the target system and network, and the OS. This allows for vulnerabilities in the system to be exploited to gain access.
- Vulnerability Scanners: Vulnerability Scanners scan systems, networks and web applications to find vulnerabilities, misconfigurations and outdated software versions, allowing us to assess how secure and strong our systems and networks are.
- Network Sniffers: In this, the tester uses tools to collect and analyze network traffic data, which hosts the network is communicating with, which protocols and ports it is communicating with, etc. This helps the tester to know whether any personal and sensitive data (such as passwords, login details, and other credentials) is flowing through the network or not.
- Web App Scanners: The tester scans the HTML, input fields and server config of the web application to find vulnerabilities like SQL injection and XSS (Cross Site Scripting) so that they can be exploited by performing attacks on them and our system can be secured.
- Password Cracker: The tester tries to crack weak passwords by using tools like brute force and wordlists so that the tester can gain access to the system or network by passing through the credentials.
